GPS Controller Scalable Cloud Infrastructure Secure Logistics India 2026
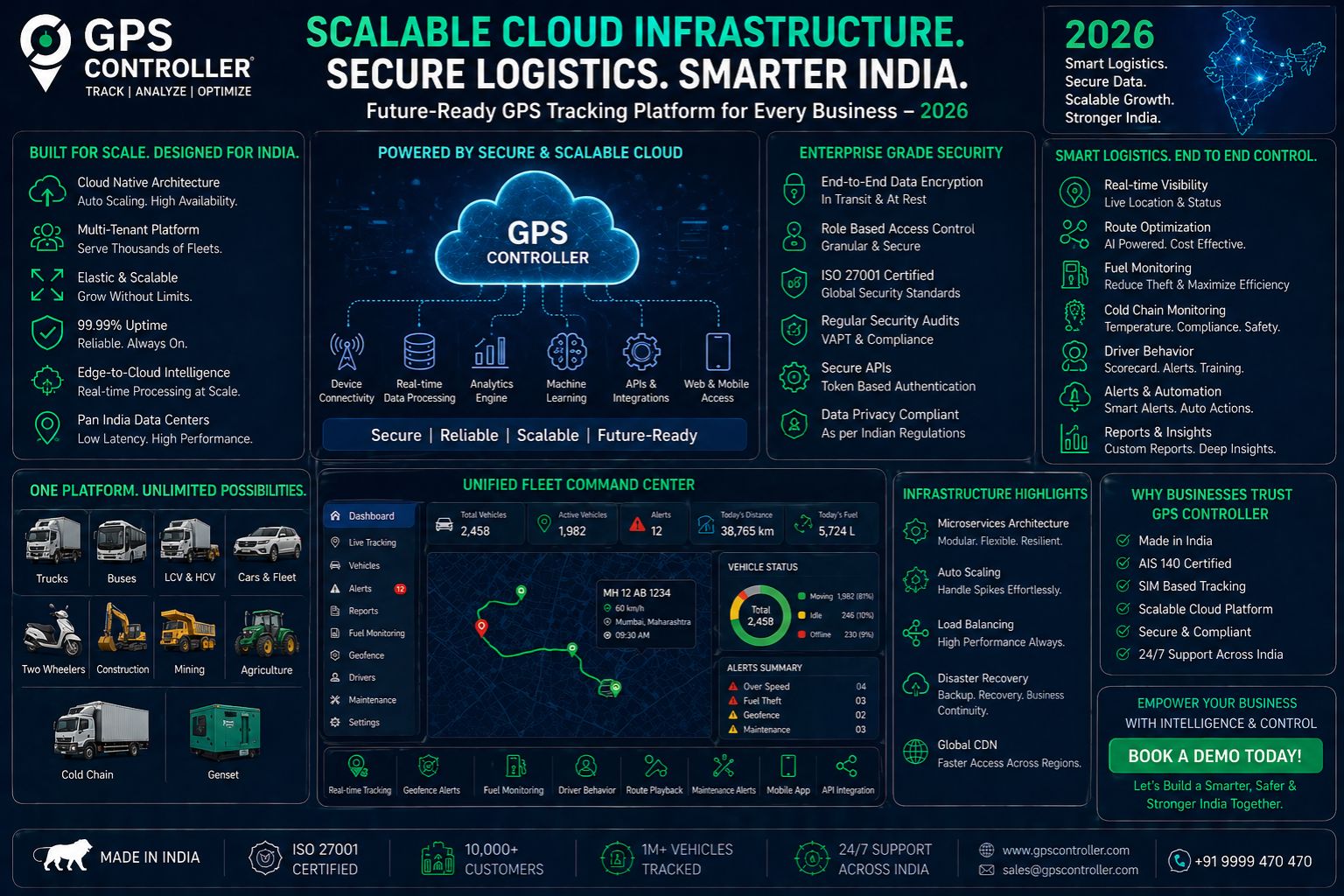
GPS Controller Scalable Cloud Infrastructure Secure Logistics India 2026
Insecure GPS controller scalable cloud infrastructure directly causes logistics failures across India in 2026, where signal latency and data corruption in vehicle telematics create compliance gaps that ripple through entire supply chains during high-volume freight movement—something many operators only realize after a missed deadline or a failed audit.
What Cloud Security Means for GPS Tracking in Indian Logistics
Secure cloud infrastructure ensures that GPS tracking data from thousands of vehicles remains uncorrupted and available in real time, but in India's variable network environment a fleet tracking platform must handle signal jitter in tunnels and delayed geofence alerts without introducing systematic errors that compound during peak dispatch hours—easier said than done when you're juggling 3,000 trucks across a dozen states.
Real Operational Risks with Scalable Infrastructure Failures
When a logistics company scales from 500 to 5,000 connected vehicles without hardened cloud architecture, location data delay becomes the norm rather than the exception, causing idle engine inaccuracies that trigger false compliance exceptions in government-mandated vehicle location logs used for inter-state freight verification; we've seen entire delivery schedules derailed by phantom idling alerts.
Common Misconceptions About Cloud Security in Fleet Tracking
Many operators assume that cloud encryption alone prevents data tampering in vehicle telematics, but the real vulnerability lies in the middleware layer where routing delay from unscaled infrastructure introduces enough latency for unauthorized geofence overrides to occur without detection, a risk that escalates when internal teams try to patch symptoms instead of redesigning the data pipeline altogether—and honestly, most teams don't even know where to start looking.
Decision Boundary for Logistics Infrastructure Investment
You must decide whether to reconfigure your existing GPS controller integration or redesign the entire cloud layer, but once your fleet exceeds 2,000 units and you encounter recurrent compliance log gaps from signal latency, internal tuning of outdated middleware will no longer suffice and you need to replace the infrastructure with a system that isolates telemetry pathways from non-critical data flows, which is where gps controller architecture becomes relevant for maintaining audit integrity—though it's not a choice you want to make mid-quarter when deliveries are piling up.
FAQ
Question: What causes GPS signal delay in Indian logistics fleets during 2026?
Answer: Signal delay primarily arises from insecure cloud infrastructure that cannot handle concurrent location data uploads from thousands of vehicles, combined with telemetry packet loss in dense urban zones and tunnel networks common across Indian freight routes—not always what you'd expect but it's the main bottleneck.
Question: How does insecure cloud infrastructure affect fleet tracking compliance?
Answer: Data corruption from unscaled cloud layers produces inaccurate compliance logs that fail government audit requirements, creating legal liability for logistics companies operating under India's 2026 vehicle tracking mandates; fines can stack up fast if your records don't match up.
Question: Can hardware upgrades fix cloud security problems in vehicle telematics?
Answer: No, hardware upgrades cannot compensate for poorly architected cloud middleware because the bottleneck is in data routing speed and encryption integrity, not device signal strength or GPS receiver sensitivity—spending on better antennas won't solve this.
Question: When should a logistics operator replace their cloud infrastructure instead of patching it?
Answer: Replace the infrastructure when you experience recurring geofence alert delays exceeding fifteen seconds across multiple vehicles simultaneously, as this indicates the architecture cannot scale to your operational load and internal fixes will not resolve the systemic routing failure—sooner is better than after an audit flag.
Comments
Post a Comment