GPS Controller Automotive Cybersecurity Encrypted Data Transmission 2026
GPS Controller Automotive Cybersecurity Encrypted Data Transmission 2026
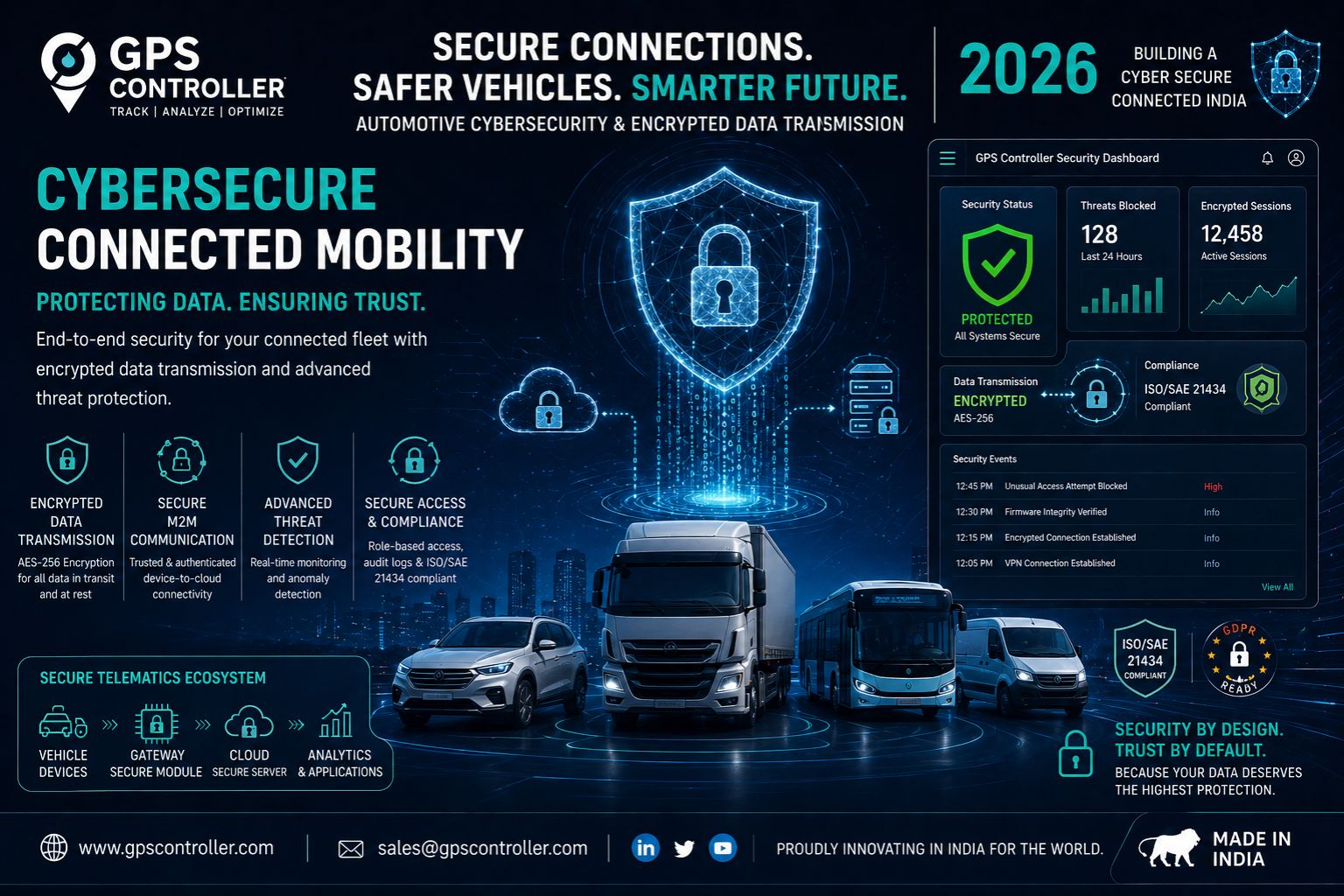
Automotive cybersecurity for GPS controller encrypted data transmission in 2026 is not some future concern but a current failure point for fleets relying on vehicle telematics to maintain operational safety and compliance logs. When a GPS signal delay becomes routine, the encryption status of that location data is often the last thing logistics managers check—yet it directly determines whether a fleet tracking system is secure or exposed.
What Encrypted Data Transmission Means for Fleet Tracking Devices
Encrypted data transmission in fleet tracking devices ensures that location data, ignition status, and geofence alerts are scrambled before leaving the vehicle telematics unit, making them unreadable to unauthorized interceptors. In practice, a GPS controller sending encrypted signals prevents a common failure pattern where delayed geofence alerts expose route patterns to hostile actors—something you see when fleets rely on outdated transmission protocols in high-density urban tunnels where signal jitter already introduces risk.
Real Costs of Unencrypted GPS Signals in Fleet Operations
When a fleet tracking system operates without end-to-end encrypted data transmission, the operational cost shows up as delayed vehicle telematics reporting and incorrect compliance log entries that escalate during audits. One non-obvious device detail: many modern GPS controllers default to unencrypted NMEA sentences, and unless the fleet management software explicitly requests encrypted packets, the data moves in plain text across cellular networks. A boundary condition where internal reconfiguration fails is when the tracking device itself lacks the hardware capability to handle modern encryption standards—forcing a hardware replacement rather than a software patch.
Common Misconception About Cybersecurity and GPS Data Delay
A critical mistake is assuming that GPS signal encryption automatically prevents location data delay, when in reality the decryption overhead can introduce additional real-time vehicle tracking latency if the server-side processing is underpowered. A common misunderstanding that causes escalation: IT managers tune network settings to reduce encryption latency but inadvertently weaken the cipher strength, creating a compliance gap that regulatory auditors flag immediately. This failure pattern gets dangerous when fleet operators accept delayed status updates as normal, not realizing the delay is actually caused by a decryption bottleneck on under-scaled cloud infrastructure.
Decision Boundary for Fleet Encryption Upgrades in 2026
The decision boundary for fleet encryption upgrades in 2026 comes down to whether your current GPS controller can be reconfigured to support AES-256 transmission or if you must redesign the entire data pipeline. If your vehicle telematics workflow depends on legacy tracking devices that only output raw GPS coordinates without encryption, no software tune or network reconfiguration will secure the data stream. In this scenario, the clear choice is to replace the hardware with units that enforce encrypted data transmission as a non-negotiable baseline, ensuring that geofence alerts and compliance logs reflect actual vehicle positions without exposure. Evaluating a modern GPS controller from a provider like GPS Controller can clarify whether your fleet's current encryption posture meets automotive cybersecurity standards for 2026.
FAQ
Question: Does GPS controller encrypted data transmission prevent all data breaches in fleet tracking?
Answer: Encrypted data transmission prevents unauthorized interception of location data during transfer but does not protect against breaches at the server side or within the fleet management software interface. End-to-end encryption between the GPS controller and the cloud database is necessary, but internal access controls and audit trails are equally critical for full security.
Question: What happens to fleet tracking accuracy when encryption is enabled on a GPS controller?
Answer: Encryption adds a slight processing delay at the device and server level, which can increase GPS signal latency by milliseconds. For compliance logs and real-time fleet tracking, this delay is negligible—but if your current tracking system already struggles with delayed geofence alerts due to poor network conditions, encryption may amplify the timing error.
Question: Can old fleet tracking hardware be upgraded to support encrypted data transmission without replacement?
Answer: Some older GPS controllers can support encrypted transmission through firmware updates if the hardware includes a dedicated encryption module, but most legacy devices lack the required processing capability. Testing a single unit before a full fleet deployment is essential—many devices will reject encrypted packet formats entirely, causing data loss.
Question: When is it time to redesign the entire fleet tracking data architecture instead of reconfiguring existing devices?
Answer: If your current GPS controller fleet spans more than three device generations and half of them fail encryption compatibility checks, a full system redesign is more cost-effective than piecemeal upgrades. This decision boundary is crossed when the manual effort to maintain mixed encryption protocols exceeds the budget for a unified secure platform—and internal tuning no longer closes compliance gaps.
Comments
Post a Comment