BeiDou frequency hopping navigation message authentication NMA explained
BeiDou frequency hopping navigation message authentication NMA explained
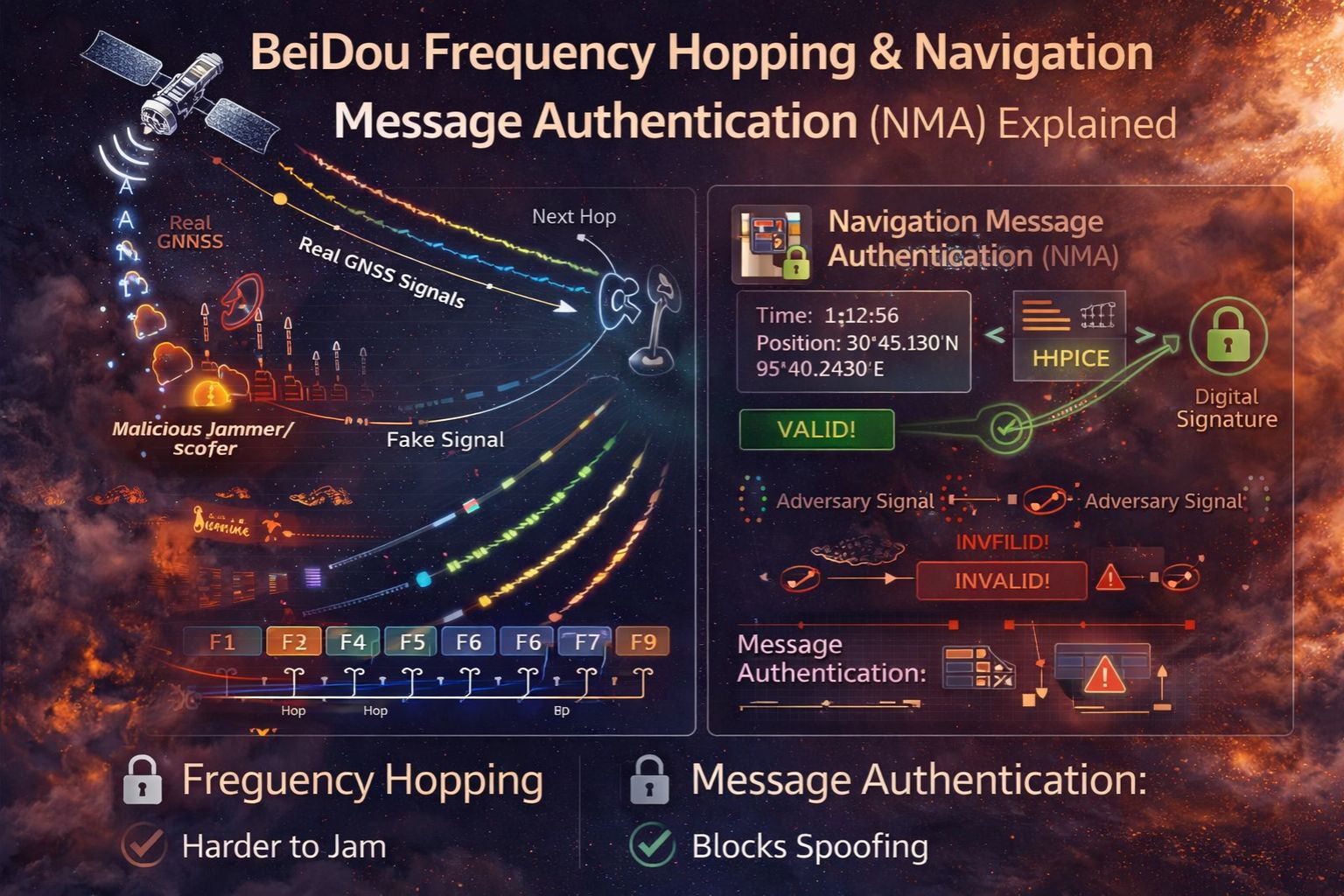
BeiDou Navigation Message Authentication (NMA) is basically a security layer that cryptographically signs satellite signals. Frequency hopping is an anti-jamming technique that rapidly switches transmission frequencies. Together, they're a core defense against spoofing attacks that could misdirect an entire fleet with false location data. For a fleet manager, this isn't about some advanced feature—it's about the fundamental trust that a vehicle's reported position is real and hasn't been messed with. That's a trust standard GPS just doesn't have, and it becomes absolutely critical when you're coordinating high-value cargo or time-sensitive deliveries. The real insight here, though, isn't in the cryptography itself. It's in understanding where this built-in signal security stops and where your own telematics system's data validation has to kick in.
Clarity: What NMA and Frequency Hopping Actually Do in Your Fleet
Think of NMA as a digital signature on every piece of location data broadcast from a BeiDou satellite. Your receiver checks this signature. If it doesn't match, the data gets thrown out, which stops a spoofer from injecting a fake "You are here" signal. Frequency hopping sort of complements this by making it way harder to jam or overpower the real signal, since it unpredictably jumps across a band. In practice, this means your tracking devices that get BeiDou signals end up with a more resilient position fix. That's especially useful in areas with a lot of interference or where someone might be trying to cause trouble. It reduces the chance of your truck's telematics system suddenly reporting it's sitting in a warehouse when it's actually barreling down the highway.
Reality Check: Operational Impact at Fleet Scale
At scale, not having these protections creates a systemic vulnerability. A fleet that relies on unauthenticated signals might not even see a spoofing event as an attack—it just logs as an unexplained route deviation, a sudden geofence breach, or some implausible idle time. I've seen telematics dashboards show a vehicle making a physically impossible jump across a city, which turned out to be from a localized spoofing test. The thing that's easy to miss is that while BeiDou's NMA secures the signal from the satellite to your device, it does nothing to secure the data *after* it reaches the device. A compromised onboard unit or a man-in-the-middle attack on the cellular backhaul can still corrupt the location data sent to your fleet management platform. That can create a false sense of security if you think authentication magically solves the entire data chain.
The Critical Mistake: Assuming Authentication is a "Set and Forget" Solution
The most common and costly misunderstanding is treating BeiDou NMA as a complete anti-spoofing solution. It's not. It authenticates the navigation message—the satellite's ephemeris and time data—but it doesn't authenticate the underlying carrier wave or ranging codes. A sophisticated spoofer can "pull" a receiver onto a false signal before introducing malicious data, in what's called a carry-off attack. On top of that, a lot of fleet tracking devices are multi-constellation (using GPS, GLONASS, Galileo, BeiDou all together). If only the BeiDou signals are authenticated but the others get spoofed, the receiver's fused position solution can still be completely corrupted. The failure pattern here is a fleet manager investing in "BeiDou-enabled" hardware, believing the whole fleet is now spoof-proof, while completely overlooking the need for system-level anomaly detection in their actual telematics data stream.
Decision Help: When to Tune, Reconfigure, or Redesign for Signal Security
Your decision really comes down to asset criticality and your threat model. For general fleet tracking, you should at least make sure your hardware supports BeiDou and that your provider's platform can log signal authentication flags—that's a *tune*. If you operate in high-risk zones or carry high-value assets, you need to *reconfigure* your telematics rules to cross-check the BeiDou position with other sensor data (like inertial measurements) and to alert on authentication failures. But there's a point where the internal fix just isn't enough, and you need a *redesign*. That's when the consequence of a single spoofing event would be catastrophic—think hazardous material transport or armored cash logistics. At that stage, you have to move beyond relying solely on satellite signal security. You need a multi-layered verification system, which likely involves gps controller logic that analyzes data consistency across the entire telematics pipeline, not just at the GNSS receiver.
FAQ
Question: Does BeiDou NMA work with all BeiDou tracking devices?
Answer: No. The device has to have a compatible BeiDou receiver chipset and firmware that can actually process the authentication message. A lot of older or cheaper devices just ignore the NMA data, so you get zero security benefit from it.
Question: Can frequency hopping prevent all GPS jamming?
Answer: It makes it much harder and more expensive for an attacker, but it's not a magic bullet. A wideband jammer that just blankets the entire frequency band can still disrupt service. Its main value is in defeating simpler, targeted jammers.
Question: How does spoofing actually affect my fleet's compliance logs?
Answer: Spoofing can create fake entries for hours-of-service (HOS) by making a moving vehicle look like it's stationary, or it can generate fraudulent geofence arrivals and departures. This corrupts ELD mandates and can absolutely lead to compliance violations during an audit, because the log data itself becomes untrustworthy.
Question: I have BeiDou devices. Is my fleet data now secure?
Answer: Not fully. Signal authentication is just the first link. Data integrity also depends on having secure device hardware, encrypted data transmission, and proper validation within your fleet software. You need a holistic security posture, which is why the better platforms integrate signal trust indicators with other telemetry to get a complete picture.
Comments
Post a Comment